How to Use Privacy Coins: A Guide to Keeping Your Bitcoin Transactions Anonymous
As the popularity of Bitcoin continues to rise, so does the concern for privacy among its users. While Bitcoin offers a level of anonymity, all transactions are recorded on a public blockchain, making it possible for savvy analysts to trace transaction histories. This is where privacy coins come into play. Coins like Monero, Zcash, and Dash employ advanced cryptographic techniques to obscure transaction details, allowing users to conduct their transactions with a greater sense of security. To use privacy coins effectively, one should start by understanding the unique features each coin offers in terms of privacy and how to acquire them.
To integrate privacy coins into your cryptocurrency transactions, follow these essential steps:
- Research and select a privacy coin: Investigate the available market options and choose a coin that aligns with your privacy needs.
- Create a secure wallet: Use a wallet that supports your chosen privacy coin while ensuring it provides robust security features.
- Buy privacy coins: Purchase your selected crypto through exchanges or peer-to-peer platforms that allow for the acquisition of privacy coins.
- Learn about coin mixing techniques: Use services that mix your coins with others to enhance your privacy further.
Counter-Strike is a highly popular first-person shooter game that pits teams of terrorists against counter-terrorists in various objective-based missions. Players can enhance their gaming experience by utilizing perks like a cloudbet promo code to access exclusive bonuses and rewards. The game has evolved significantly since its initial release, becoming a staple in the esports community with competitive tournaments worldwide.
The Art of Mixing: Exploring Bitcoin Tumblers and Their Effectiveness
The process of mixing cryptocurrencies, particularly Bitcoin, has gained prominence in discussions around privacy and security in the world of digital currency. Bitcoin tumblers, also known as mixing services, serve as a crucial tool for users who wish to obscure the transaction history of their Bitcoin. By effectively pooling together various users' coins and redistributing them in a manner that complicates the traceability of transactions, these services enhance the privacy of individuals who may have legitimate reasons to maintain anonymity. Additionally, the effectiveness of these tumblers can vary significantly, influenced by factors like service reputation, mixing algorithms, and transaction volume.
However, the use of Bitcoin tumblers is not without controversy. Many law enforcement agencies view these services with scrutiny, as they can potentially facilitate illegal activities by making it difficult to trace funds back to their original source. Consequently, potential users must weigh the heightened privacy benefits against the risks associated with using unverified tumblers. In this landscape, research becomes paramount—understanding how different tumblers operate, reading user reviews, and evaluating their compliance with regulations can help users make informed decisions about utilizing these services for effective privacy management.
Understanding the Risks: What You Need to Know About Bitcoin Transaction Privacy
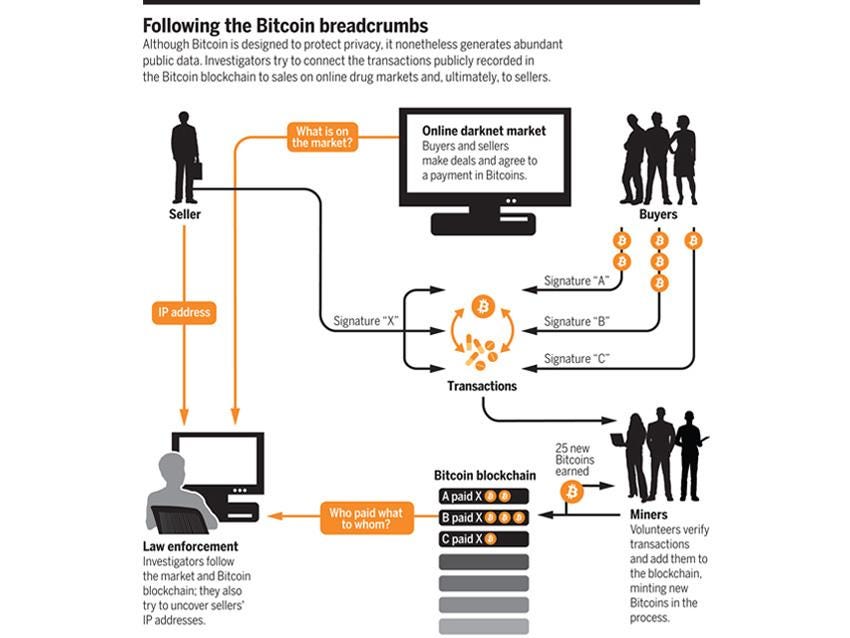
As the popularity of Bitcoin continues to rise, it is essential to understand the inherent risks associated with Bitcoin transaction privacy. Unlike traditional financial systems, Bitcoin operates on a public ledger known as the blockchain, where all transactions are recorded and can be viewed by anyone. While this transparency can enhance security, it can also compromise the anonymity of users. Detailed transaction histories can potentially link users to their wallets, exposing personal information or spending habits. Therefore, users must be aware of these risks when engaging in any Bitcoin transactions.
To enhance your Bitcoin transaction privacy, consider implementing various strategies. Here are a few effective methods:
- Use a Bitcoin mixer to obscure the transaction trail.
- Employ addresses that change with each transaction to limit address reuse.
- Utilize privacy-focused wallets that integrate additional security features.
- Be cautious with your online presence and sharing of wallet addresses.